The Fifth International Symposium on
The Fifth International Symposium on
Innovation in Information and Communication Technology [ISIICT 2018]
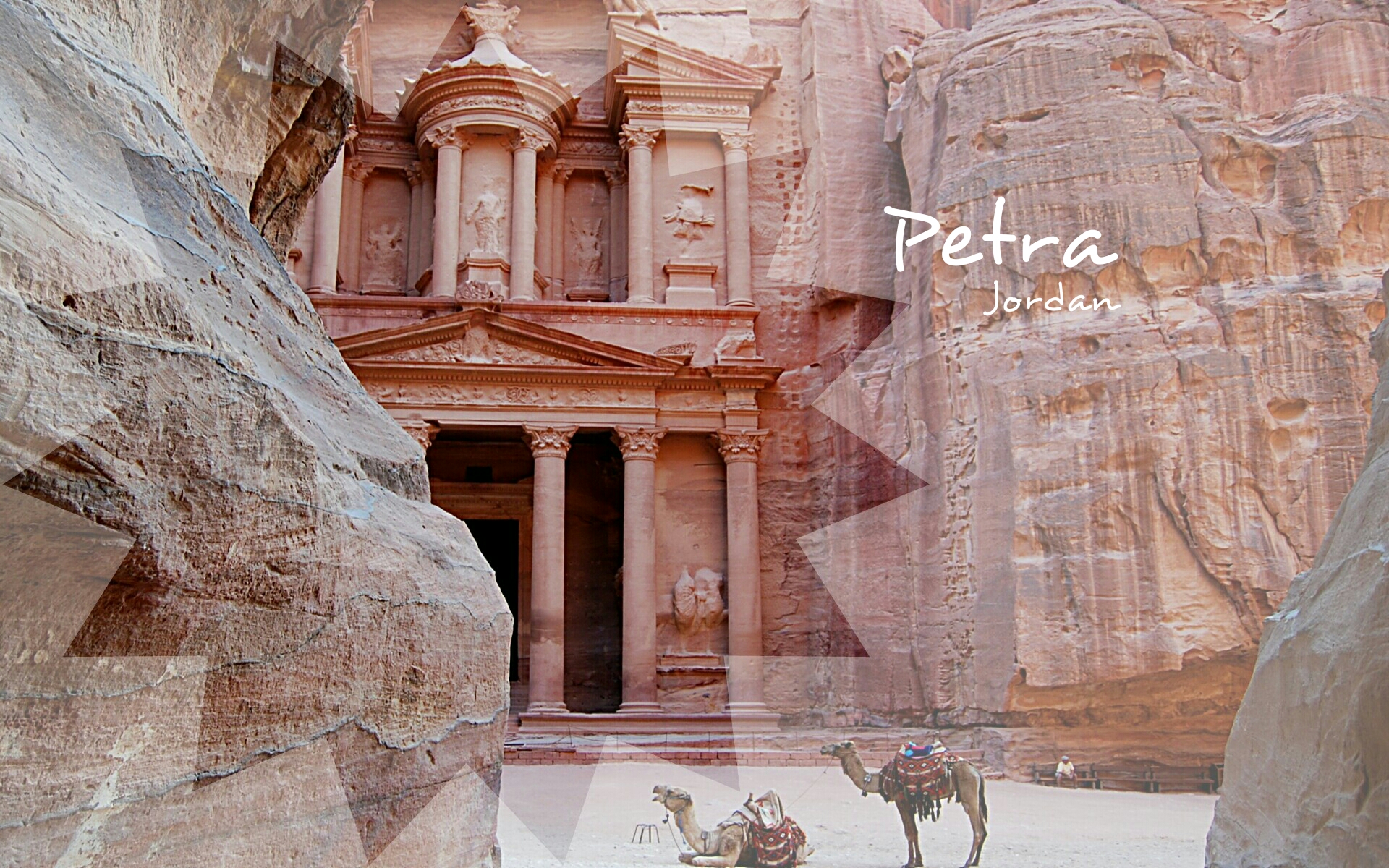
October 31 - November 01, 2018
The Fifth International Symposium on Innovation in Information and Communication Technology (ISIICT 2018)
October 31 - November 01, 2018 , Philadelphia University, Amman, Jordan
UPCOMING DEADLINES
Papers
- Submission of Papers:
24/09/2018 - Notification of Acceptance: 28/09/2018
- Final Submission (Camera Ready): 05/10/2018
- Early Registration Deadline: 01/10/2018
The symposium is intended to serve as a hub to identify emerging research topics, and define the future of Information and Communication Technologies.
The technical program of The ISIICT 2018 will include a Research Track, an Application Track, and a Short Paper Track. Theoretical and technical contributions addressing all areas related to systems, applications and innovations are solicited. Papers on the new generation of Utility Computing, including cloud and edge computing, are particularly welcome. Tutorials and panel discussions on the challenges brought by these technologies will be organised. All submissions will be refereed by at least three members of the Programme Committee.
Symposium Areas
(Not limited to):
- Theme 1: Cloud-based Systems
- Cloud as a Service
- Cloud applications
- Cloud infrastructure
- Cloud management and operations
- Cloud economics
- Fog and edge computing
- Microservices
- Case studies
- Theme 2: Embedded Systems and the IoT
- Development methods for Embedded Systems and IoT
- Platforms for Embedded Systems and IoT
- Embedded Systems and IoT Applications
- Energy efficiency
- Adaptation and control
- Case studies
- Theme 3: Big Data
- Big Data and Emerging Technologies (IoT, Mobile, Social)
- Business Intelligence and Analytics
- Data Engineering and Architecture
- Data Governance and Protection
- Data Visualisation
- Governance and Regulation
- Tools for Complex Workloads
- Machine Learning and Deep Learning
- Case studies
- Theme 4: Software Technologies
- Software engineering
- Management in agile contexts
- Software management tools and techniques
- Enterprise Systems and Applications
- Software analytics
- Green software management
- Programming models
- Agent and Multi-agent Systems
- Mobile Apps
- Real-time Systems
- Case studies and industry experience
- Theme 5: Security
- Cryptography and data protection
- Peer-to-peer security
- Security of wireless sensor networks
- Security of Cyber Physical Systems
- Security of Internet of Things solutions
- Privacy-enhancing methods
- Cryptographic protocols
- Security as quality of service, quality of protection
- Security models, evaluation, and verification
- Formal methods in security
- Trust and reputation models
- Security of Smart Grid systems
- Case studies
- Theme 6: Performance Engineering
- Performance-oriented design and analysis methods
- Formal modelling paradigms
- Solution and simplification techniques for stochastic processes
- Model checking and validation
- Simulation techniques and experimental design
- Benchmarks and benchmark evaluation
- Performance tools
- Theme 7: Mobile and Wireless Networks
- Recent Trends in Mobile and Wireless Applications
- Wireless, Mobile Networks & Applications
- Mobile Ad Hoc and Sensor Networks
- Architectures, Protocols, and Algorithms for Mobile & Wireless Networks
- Cryptography, Security and Privacy of Mobile & Wireless Networks
- Data Management on Mobile and Wireless Computing
- Distributed Algorithms of Mobile Computing
- Energy efficiency
- Performance of Mobile and Wireless Networks and Systems
- Resource Management in Mobile, Wireless and Ad-Hoc Networks
- Wireless Multimedia Systems
- Ubiquitous Computing
- Theme 8: Bio-Inspired Computing
- Molecular computing
- Quantum computing
- Optical computing
- Self-assembling and self-organizing systems
- Cellular automata
- Neural computation
- Evolutionary computation
- Swarm intelligence
- Ant algorithms
- Artificial immune systems
- Computational systems biology
- Computational neuroscience
- Theme 9: Bio-Medical Computing
- Data and Signal Acquisition
- Robotics and Medicine
- Biomedical Electronics
- Modelling and simulation
- Surgery Simulation
- Virtual Reality
- Medical Image Processing
- Optical Imaging
- Case studies
- Theme 10: Web Computing
- Ontology and Semantic Web for Services Computing
- Business process integration and management
- Service discovery, composition, and recommendation
- Service operations, management, and governance
- Service applications and implementations
- Business intelligence, analytics and economics for services
- E-commerce applications
- Quality of Service
- Case studies
- Theme 11: Natural Language Processing
- Cognitive modelling
- Document analysis: categorization, topic models, and retrieval
- Information extraction, text mining
- Machine learning in NLP
- Machine translation
- Semantics
- Sentiment analysis and opinion mining
- Social media
- Speech
- Case studies
General Chair
Karim Djemame, University of Leeds, UK
Organizing Chair
Mohamed Bettaz, Philadelphia University, Jordan
Organizing Co-Chair
Sunil Kumar Khatri, Amity Institute of Information Technology, India
Coordination Chair
Mourad Maouche, Philadelphia University, Jordan
Technical Sponsor